FHE: The Holy Grail of On-Chain Privacy?
10 feb 2026 · 6 min read
Fully Homomorphic Encryption (FHE) is gaining attention for letting applications compute on private data without ever revealing it.
But does it actually make crypto private, or is it just hype?
At the core of this promise is a concept known as Homomorphic Encryption (HE)
Homomorphic Encryption
HE is a cryptographic technique that allows computations to be performed on encrypted data without requiring decryption.
Depending on the level of computation supported, HE is classified into several schemes.
- Partially Homomorphic Encryption (PHE)
Supports only a single operation, such as addition or multiplication, on encrypted data. - Somewhat Homomorphic Encryption (SHE)
Supports limited additions and multiplications, but only for shallow or small computations. - Leveled Fully Homomorphic Encryption (Leveled FHE)
Supports complex computations up to a fixed depth, without requiring bootstrapping. - Fully Homomorphic Encryption (FHE)
Supports unlimited, arbitrary computation on encrypted data without decryption.
Among these, FHE is the only scheme that enables fully general computation on encrypted data.
What Makes Fully Homomorphic Encryption (FHE) Different
Fully Homomorphic Encryption (FHE) enables computation directly over encrypted data (ciphertext) without exposing plaintext at any point.
Earlier homomorphic encryption schemes protect data at rest (stored) and in transit (in motion), but still require decryption when data is in use (actively processed), creating a clear privacy boundary.
FHE eliminates this boundary by preserving encryption throughout computation, enabling secure processing even in untrusted execution environments.
Core Properties of FHE
- Privacy-Preserving Computation
Data remains encrypted throughout processing, even on untrusted systems.
- Arbitrary Computation
FHE supports both addition and multiplication, enabling general-purpose computation.
- Bootstrapping
Refreshes ciphertexts by reducing noise (encryption error), allowing continuous computation.
- Applications
Used in encrypted machine learning, secure cloud workloads, financial analytics, and private smart contracts.
How FHE Achieves Computation
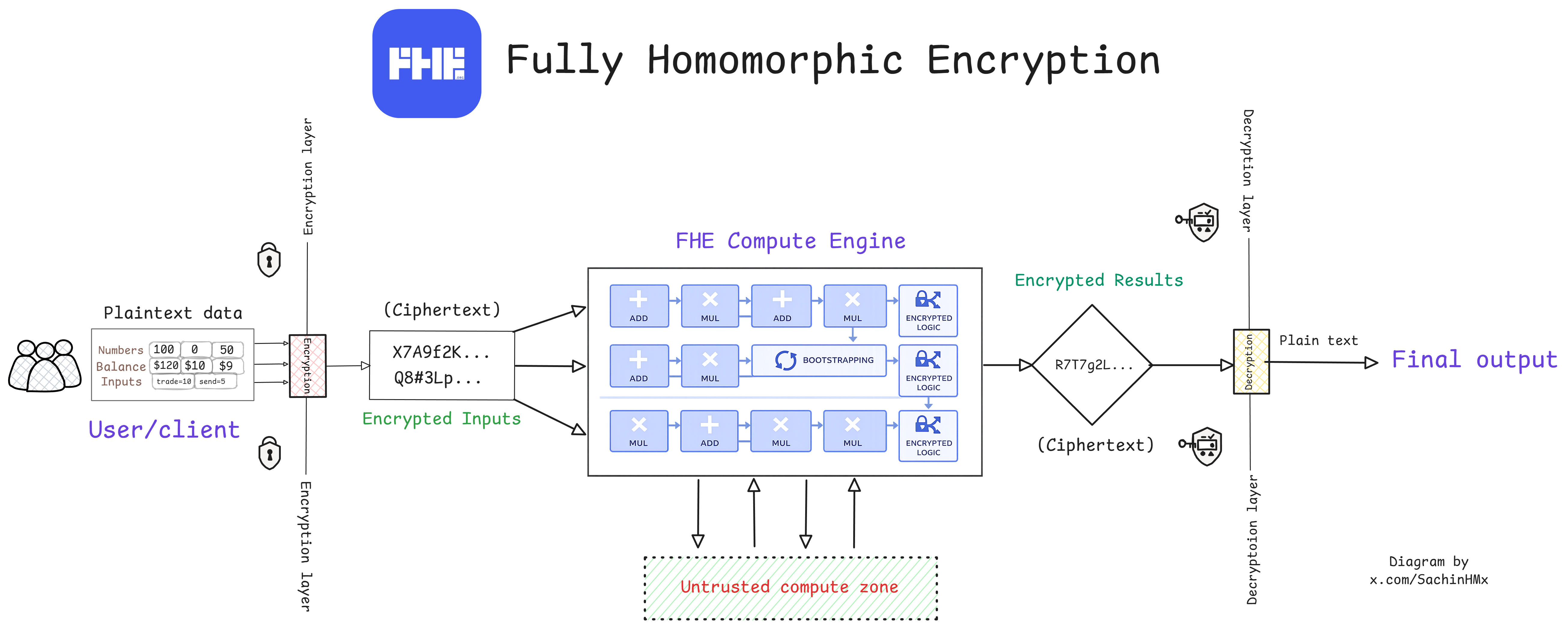
Fig: Visual overview of Fully Homomorphic Encryption showing encrypted computation inside an untrusted execution environment.
FHE allows encrypted inputs to be processed directly without ever revealing the original plaintext.
User → Plaintext Input → Encrypted Inputs → FHE Compute Engine (homomorphic operations) → Encrypted Outputs → Plaintext Output
Only ciphertext enters the compute engine, removing the need to trust infrastructure or hardware.
Homomorphic operations combined with bootstrapping enable complex encrypted computations, with decryption only at the final output.
Key Challenges Facing FHE Today
Performance Overhead
Encrypted computation is 1,000×–10,000× slower than plaintext, mainly due to bootstrapping.
Reliance on MPC Committees
Most FHE systems still depend on MPC committees (FHEVM-style systems) for key management and output decryption.
Competition from Other Privacy Tech
ZKPs, MPC, and TEEs often deliver better performance today, but with composability or trust trade-offs.
Verifiability Gap (vFHE still immature)
FHE lacks native correctness proofs; verifiable FHE remains early and computationally expensive.
What changes next
Hardware acceleration is now closing the performance gap and pushing FHE toward real-world usability.
Hardware Acceleration: Making FHE Practical
Without hardware acceleration, FHE remains largely theoretical and confined to research environments.
With hardware acceleration, FHE becomes usable for real-world applications across blockchain and AI.
What Makes FHE Computation Heavy
FHE relies on extremely expensive mathematical operations, including:
- Polynomial arithmetic
- Modular multiplication
- Number-theoretic transforms (NTTs)
- Bootstrapping (noise refresh)
These operations introduce massive overhead in software-based implementations.
What’s Driving FHE Performance Improvements
The widely discussed 10× performance gains in FHE come from successive hardware transitions:
CPU → GPU → FPGA → ASIC
Each shift delivers roughly 10×–100× efficiency improvements, resulting in real-world breakthroughs:
- Bootstrapping latency dropped from minutes to milliseconds
- Throughput scaled from near-single operations (~1 TPS) to 100,000+ TPS
This progress reflects hardware evolution, not incremental software tweaks.
The Core Shift
- Software FHE → slow and limited
- Hardware-accelerated FHE → practical and scalable
Bootstrapping made FHE slow. Hardware acceleration is what makes FHE real.
As performance improves, FHE is moving from niche cryptography toward production-grade privacy infrastructure.
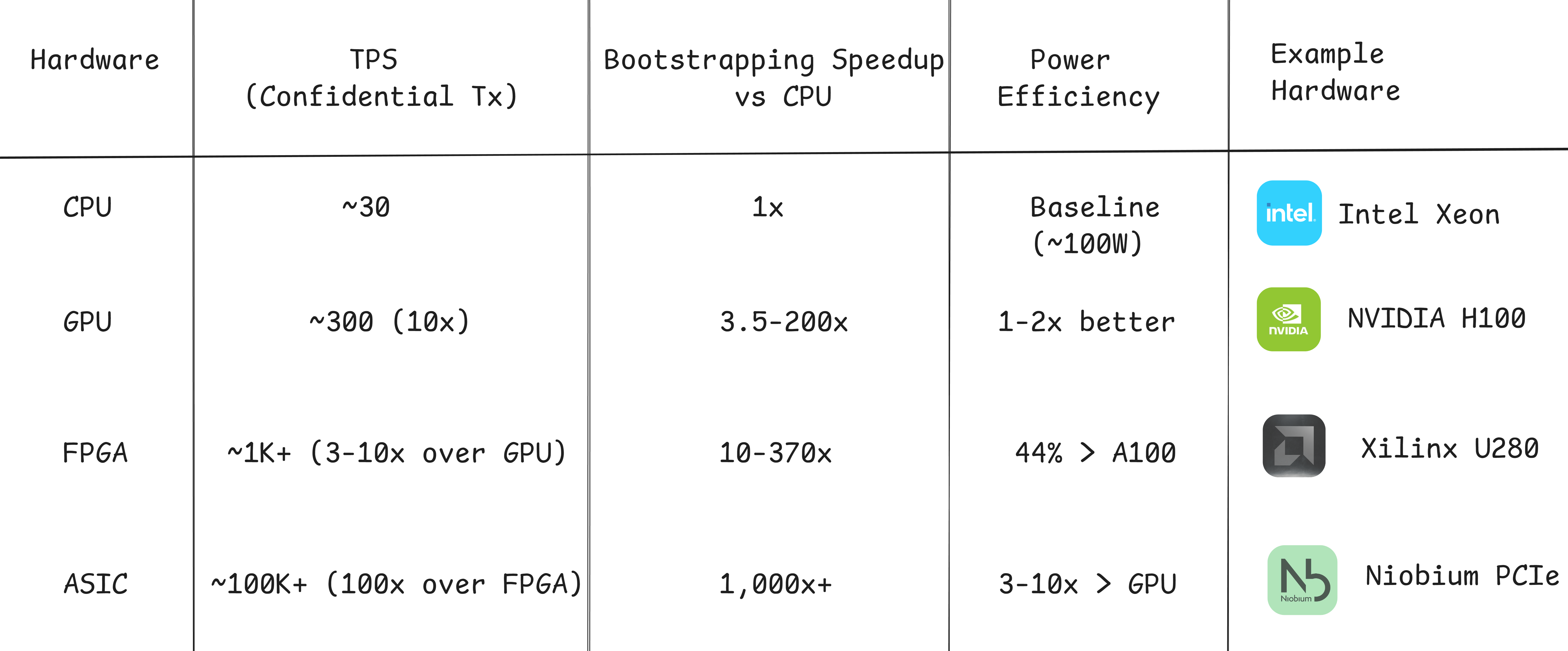
Fig: Performance progression of FHE across CPU, GPU, FPGA, and ASIC hardware acceleration.
FHE-Enhanced Systems
These systems extend base FHE with verifiability, blockchain execution layers, or off-chain coprocessors to make encrypted computation usable in practice.
vFHE (Verifiable Fully Homomorphic Encryption)
Adds cryptographic proofs to verify that encrypted computations were executed correctly on untrusted infrastructure.
Use cases: zkOpenFHE research framework (EPFL), verifiable encrypted cloud computation, and auditable private AI workloads.
fhEVM (FHE for Ethereum Virtual Machine)
Integrates FHE directly into EVM smart contracts, enabling encrypted on-chain state and confidential execution.
Use cases: confidential DeFi and encrypted smart contracts built using fhEVM by @zama.
zkEVHE / zkFHE (Zero-Knowledge Enhanced FHE)
Combines FHE with zero-knowledge proofs to provide succinct, non-interactive verification of encrypted computation.
Use cases: zkOpenFHE proving pipelines, privacy-preserving AI inference with auditability.
CoFHE (FHE Coprocessor Architecture)
Executes encrypted computation off-chain and verifies results on-chain to avoid FHE’s on-chain performance cost.
Use cases: private DeFi, encrypted transactions, and real-time confidential apps built by @fhenix.
FHE + MPC Hybrid Systems
Use FHE for encrypted computation while relying on MPC committees for key management and output decryption.
Use cases: most current FHE blockchain deployments, including fhEVM-style systems and CoFHE-based flows.
- Pure FHE is rarely deployed alone today.
FHE today extends beyond cryptography into an emerging ecosystem of infrastructure, private blockchains, DeFi applications, and encrypted AI systems.
The Future of FHE
FHE is evolving toward systems that are secure, efficient, and fully trustless.
- Post-Quantum FHE
Lattice-based schemes make FHE naturally quantum-resistant. - Approximate FHE (AI & ML)
Schemes like CKKS trade precision for speed, enabling encrypted machine learning. - Verifiability & iO Integration
Recent research, including Scalable Private World Computer via Root iO by the Ethereum Foundation, explores combining FHE with indistinguishability obfuscation to reduce reliance on MPC committees and enable fully trustless private computation.
Why This Matters
FHE enables computation directly on encrypted data, not just hidden transactions.
What once ran 1,000×–10,000× slower is now reaching 100,000+ TPS through hardware acceleration.
With over $1.5B invested, FHE is moving from academic theory to real privacy infrastructure.
As this transition unfolds, FHE has the potential to redefine how data is used, shared, and secured across finance, AI, and decentralized systems.